A Bayesian Algorithm to Enhance Resilience of WAMS Applications Against Cyber Attacks
Research Fellow: Haris M. Khalid | Advisor: Jimmy C.-H. Peng | Project Duration: 2015 -2016
Monitoring critical infrastructures is highly dependent on the accuracy of the installed sensors and the robustness of estimation algorithms. Data-injection attacks can degrade the operational reliability and security of any cyber-physical infrastructures. An attacker can compromise the integrity of the monitoring algorithms by hijacking a subset of sensor measurements (i.e. from PMUs), and sending manipulated readings as shown in Figure 1. Such approach can result in wide-area blackouts in power grids.
In the context of smart grid, it is challenging to detect malicious data-attacks as an adversary can choose the site of attack judiciously and design the attack data carefully. In the recent literature, several methods have been proposed to identify abnormal data segments and isolate attacked sensors. However, most techniques have been published to enhance state estimation - an application used to determine the steady-state operating point of a grid. Few have been proposed for Wide Area Monitoring System (WAMS) applications, and thus is the scope of this work. Note that WAMS focuses on monitoring fast network transients. False information could be given to delay control actions, which can result to system-wide blackouts.

Figure 1. Illustrative example of an attack injecting malicious data to desired locations within a grid.
Among WAMS applications, oscillation detection is one of the most mature and widely adopted function. It has been installed in the control centers of many transmission utilities to monitor the damping of electromechanical oscillations in critical tie-lines. The damping dynamics are highly complex in any interconnected systems, and often the resultant damping ratio of oscillations are unknown due to the large number of involved equipment. It is therefore challenging to identify falsely extracted information from malicious measurements, and thus making oscillation detection an attractive target to attack.
Furthermore, injecting measurements to hide unstable inter-area oscillations can potentially lead to wide-area blackouts and system breakups as seen in the Northwestern blackout in the USA in 1996. Hence, oscillation detection serves as an ideal candidate example. In this work, data-injection attacks are assumed to take place in an advanced sensing device known as Phasor Measurement Units (PMUs) installed in transmission substations.
Problem Statement
In an event of an attack, the following two negative consequences can occur due to inaccurate monitoring and time complexity of the algorithms. 1) If the data is altered in a way that is not detectable as false dynamics by monitoring schemes, the perceived observable state of the system will be wrong. This will then lead to improper control actions, which may endanger the security of the system. 2) The malicious intent might not be to hide the attack, but to force part of the system to become unobservable due to the collective behavior among the network of nodes. This can blind the system operators and increase the vulnerability of the grid to further attacks or inappropriate operations. More importantly, regardless to any consequences, the impacts of acting on incorrect or missing information will have already propagated into the rest of the system. At this stage, it may already be too late to avoid a wide-area power outage within the grid.
The proposed Baysian-based Approximated Filter (BAF) is summarised into a pseudo code as seen in Algorithm 1. The variables used in the code are defined from Line 1 to 13. This is followed by the extraction of model from the PMU measurements at each i-th location. A for loop is applied to calculate the information about the model information, electromechanical oscillations, developing attack vectors, data injection detection, and the Bayesian-based approximation filter from each location. These loops can be seen in Line 14 to 17, 18 to 20, 21 to 23, and 24 to 27 respectively. Once the information is collected from each PMU, a for loop for the distributed fusion center is applied to compute all the local measurements. This requires a cumulative for loop as shown in Line 28 to 31. The final model extraction takes place in Line 32–33, where results about estimated eigenvalues, oscillatory frequencies, and damping factors are then calculated.
Case Study 1: New Zealand Grid
The operation of the Bayesian-based approximation filter (BAF) is first evaluated using recorded measurements collected from the New Zealand transmission grid. The network consists of a combination of 400 kV, 220 kV, and 110 kV lines that are interconnected by HVDC links between the North and South Islands. Recorded measurements were collected from North Makarewa (NMA) and Twizel (TWZ) substations between 11:14:40 to 11:15:40 on 30 July 2008. Two oscillations (0.61 Hz and 0.75Hz) have been identified within the measurements.

The aim of this test case is to validate the fundamental capability of the proposed scheme. Therefore, the implemented attacks will be limited to random and controlled data injections at North Makarewa substation. The random scenario injects white noise, whereas the controlled situation is a smarter attack making one oscillation exhibits a higher damping ratio. The intention is to mislead the operators of believing the grid is more stable, and thus delaying the supplementary damping actions. Meanwhile, the assumption is data-injection attacks intercept communication transmission or tempering the PMU with the objective to replace original measurements with manipulated values. The resultant simulated attacks are shown in Figure 2.

Figure 2. Simulated attacks that corrupted PMU measurements at NMA substation in New Zealand.
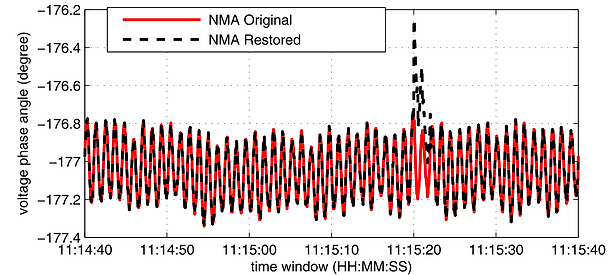
Figure 3. Recovered PMU measurements using the proposed BAF.
BAF demonstrates adequate resilience against both attacks. Its ability to manage the information loss after identifying abnormal measurements minimized the impact of an attack on extracted oscillatory parameters. This is due to the property of designed filter, which can handle the probability densities of information even with less samples. Furthermore, MSE values are fairly consistent throughout the monitoring windows and are in the magnitude of 0.001. The consistent accuracy during the first and second attack shows the injected measurements generate little threats to the reliability and security of the monitoring solutions. The recursive nature of BAF, with its novelty to tackle the information loss, allows it to reconstruct the original profile of the NMA as shown in Figure 3.
Case Study 2: Oman Electricity Grid
To further evaluate the performance of the proposed scheme, a simulated transmission network of Oman has been used involving 231 Buses. The existing transmission network covers the northern Oman, and is connected with the United Arab Emirates grid. The backbone of Oman system consists of 132 kV and 220 kV lines.
In this study, the network parameters are based on the projected 2015 summer peak demand scenario. A total of 25 PMUs have been installed across the simulated grid. All loads are continuously being perturbed with small power fluctuations of up to 1% of their nominal values. In addition, two three-phase-short-circuit faults were introduced during the simulation. The purpose of this study is to evaluate the capability of BAF to distinguish transient faults and intentional attacks. The corrupted measurements collected at Barka substation are shown in Figure 4, while restored dynamics are illustrated in Figure 5. Overall, BAF is able to capture true network transients and subsequently extract the stability parameters.

Figure 4. Simulated attacks that corrupted PMU measurements at Barka substation in Oman.

Figure 5. Recovered PMU measurements using the proposed BAF.
In summary, a Bayesian-based approximation filter has been proposed and demonstrated to improve the immunity of the monitoring applications against data-injection attacks. The predictive distribution property of the algorithm has helped to monitor power oscillation even in the presence of information loss. Mathematical derivations demonstrated the ability to identify attacks through interactions with neighboring monitoring nodes. In this paper, the proposed scheme has been applied to a mature wide-area monitoring application known as oscillation detection. Manipulating recorded and simulated measurements collected from PMU, the proposed method was able to extract accurate oscillatory parameters in the presence of data-injection attacks. Integration of the proposed immunity scheme in other WAMS applications will be evaluated in the future.